Cipla Hit by Akira Ransomware: 70GB of Sensitive Data Allegedly Stolen
Dec 11, 2024
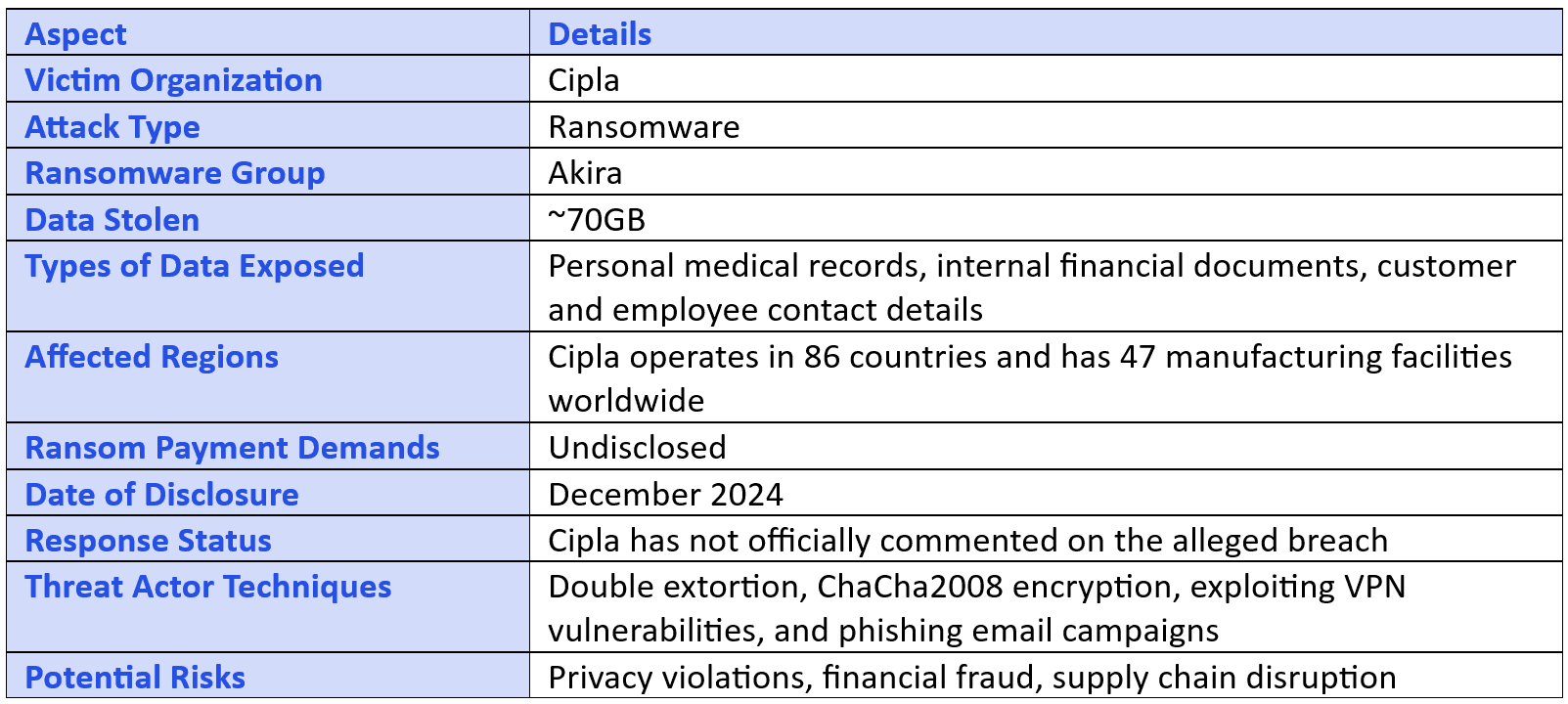
In a significant cybersecurity incident, Indian pharmaceutical giant Cipla has reportedly fallen victim to a cyberattack orchestrated by the Akira ransomware group. The attackers claim to have exfiltrated approximately 70GB of sensitive data from the company, which operates 47 manufacturing facilities worldwide and distributes products across 86 countries.
Incident Overview
The Akira ransomware group announced the breach on their dark web portal, asserting that they had successfully stolen a substantial amount of data from Cipla. This disclosure was highlighted by cybersecurity analysts who routinely monitor ransomware activities.
Nature of the Compromised Data
The stolen data reportedly encompasses a wide array of sensitive information, including:
Personal Medical Records: Details of patients' prescribed medications and health information.
Internal Financial Information: Confidential financial documents, invoices, and transactions.
Customer Contacts: Names, phone numbers, and email addresses of Cipla’s clients worldwide.
Employee Contact Details: Personal information, including email addresses and phone numbers of Cipla employees.
The exposure of such data raises significant concerns regarding patient privacy, corporate confidentiality, and the potential misuse of personal and financial information by malicious actors.
About the Akira Ransomware Group
Emerging in the first quarter of 2023, the Akira ransomware group has quickly established itself as a major threat actor in the cybersecurity landscape. The group has reportedly impacted over 350 organizations across various industries.
Akira is notorious for its use of sophisticated techniques, including:
ChaCha2008 Encryption: A robust encryption algorithm used to lock victims' data, making it inaccessible without the decryption key.
Distribution Methods: Utilizing phishing email attachments and exploiting VPN vulnerabilities to infiltrate organizational networks.
The group employs a double extortion strategy, where they not only encrypt the victim’s files but also exfiltrate sensitive data. This tactic pressures organizations to pay the ransom under the threat of public data exposure.
Cipla's Response and Industry Implications
As of now, Cipla has not publicly confirmed the breach or commented on the ransomware group’s claims. If validated, this breach underscores the pressing need for enhanced cybersecurity measures within the pharmaceutical sector, particularly given Cipla’s significant role in the global supply chain.
The potential exposure of personal medical records and financial information could have far-reaching consequences for the company, its employees, and its customers. This incident serves as a stark reminder of the vulnerabilities in critical industries and the importance of implementing proactive cybersecurity strategies.
Recommendations for Organizations
In light of increasing ransomware attacks targeting critical sectors, cybersecurity experts recommend organizations adopt robust prevention strategies, including:
Regular Security Audits: Conducting frequent assessments to identify and mitigate vulnerabilities in IT systems.
Employee Training: Ensuring staff are educated on cybersecurity best practices, particularly around recognizing phishing attempts.
Advanced Endpoint Protection: Deploying state-of-the-art tools to monitor and prevent malicious activities.
Proactive measures like these are essential to safeguard sensitive information and maintain trust in an organization’s operations.
Disclaimer: ClearPhish maintains a strict policy of not participating in the theft, distribution, or handling of stolen data or files. The platform does not engage in exfiltration, downloading, hosting, or reposting any illegally obtained information. Any responsibility or legal inquiries regarding the data should be directed solely at the responsible cybercriminals or attackers, as ClearPhish is not involved in these activities. We encourage parties affected by any breach to seek resolution through legal channels directly with the attackers responsible for such incidents.