Critical Moxa Device Vulnerabilities Expose Industrial Networks: Update Now to Stay Secure
Jan 9, 2025
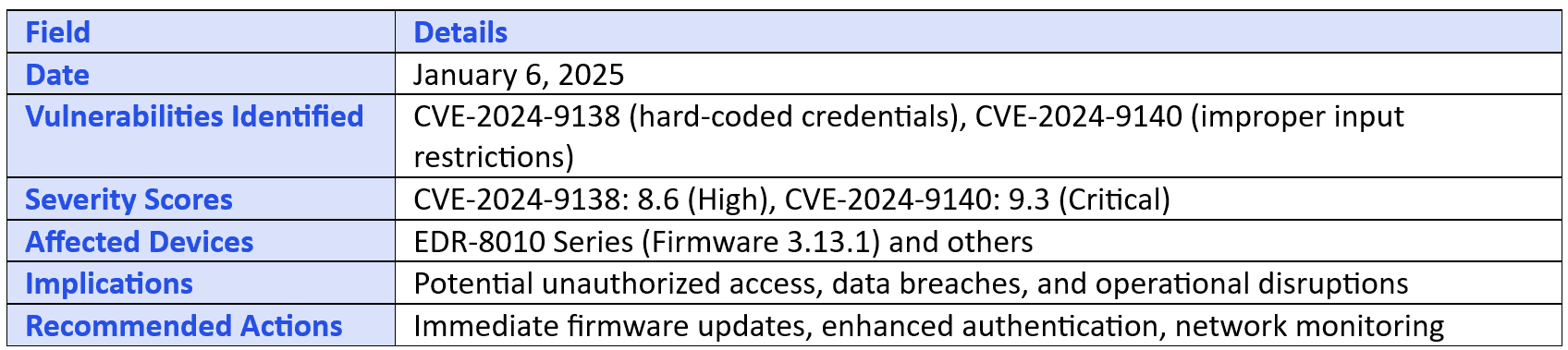
On January 6, 2025, industrial networking and communications provider Moxa issued an urgent security advisory concerning two critical vulnerabilities affecting several of its devices.
Vulnerabilities Identified:
CVE-2024-9138: A high-severity flaw (CVSS score: 8.6) involving hard-coded credentials that could allow authenticated users to escalate privileges to root.
CVE-2024-9140: A critical vulnerability (CVSS score: 9.3) stemming from improper input restrictions, enabling remote attackers to execute arbitrary commands, potentially leading to full system compromise.
Affected Devices:
The vulnerabilities impact various models of Moxa's cellular routers, secure routers, and network security appliances, including:
Devices Impacted by Both CVE-2024-9140 and CVE-2024-9138:
EDR-8010 Series (Firmware 3.13.1 and earlier)
EDR-G9004 Series (Firmware 3.13.1 and earlier)
EDR-G9010 Series (Firmware 3.13.1 and earlier)
EDF-G1002-BP Series (Firmware 3.13.1 and earlier)
NAT-102 Series (Firmware 1.0.5 and earlier)
OnCell G4302-LTE4 Series (Firmware 3.13 and earlier)
TN-4900 Series (Firmware 3.13 and earlier)
Devices Impacted Only by CVE-2024-9138:
EDR-810 Series (Firmware 5.12.37 and earlier)
EDR-G902 Series (Firmware 5.7.25 and earlier)
TN-4900 Series (Firmware 3.13 and earlier)
Recommended Actions:
Moxa has released firmware updates to address these vulnerabilities and strongly recommends immediate action to prevent potential exploitation.
EDR-8010 Series, EDR-G9004 Series, EDR-G9010 Series, EDF-G1002-BP Series: Update to Firmware Version 3.14 (Released on December 31, 2024).
Implications for Industrial Networks:
Moxa devices are integral to industrial automation and control systems across sectors such as transportation, utilities, energy, and telecommunications. Exploitation of these vulnerabilities could lead to unauthorized access, data breaches, and operational disruptions, underscoring the critical need for timely patching and robust security measures.
Key Takeaways:
Prompt Updates: Regularly apply firmware updates to mitigate known vulnerabilities.
Access Controls: Implement strong authentication mechanisms to prevent unauthorized access.
Network Monitoring: Continuously monitor network traffic for unusual activities indicative of potential breaches.
This incident highlights the importance of proactive cybersecurity practices in safeguarding industrial networks against evolving threats.
Disclaimer: ClearPhish maintains a strict policy of not participating in the theft, distribution, or handling of stolen data or files. The platform does not engage in exfiltration, downloading, hosting, or reposting any illegally obtained information. Any responsibility or legal inquiries regarding the data should be directed solely at the responsible cybercriminals or attackers, as ClearPhish is not involved in these activities. We encourage parties affected by any breach to seek resolution through legal channels directly with the attackers responsible for such incidents.